

What is Information security?
Security means surety of not breaching personal information. It is also known as safeguard or the bail. Information security means we are protecting our self or our personal data from the unauthorized access, data modification, data disclosure or the data breaching. Information security is an essential part of the IT field or IT business.
Why information security is needed?
Information (data, file or any kind of handy document) is the life of any business organization in this today’s digital world, where labor work converted into technical world and documents are converted into Data or information. Every big organization includes many departments within it like Development, Research and all that. High quality information is reached to the customer or the human via marketing, push digital marketing as well as pull digital marketing.
Now simple question comes to mind that what is the guarantee of this system that it is reliable and honest to us? This question inspires us to build an Information Security system which guarantees us of the safeguard of our Data or the information.
Information Security for the Organization
Information security is not only the matter of passwords and usernames. It includes many parts within it which are categorized in a layer system. There is major tow layers come in that.
Application Layer: This layer includes security of the client side as well as the application. Username password comes in this layer also the data breaches of any information of the organization comes in this. Network Layer: This layer includes the security on the network layer. It assures us of the security of modem, router and the big servers to not be compromised. At network layer there are lots of exploits which are performed on the application or the browser side, which has an ability to hack the database of a particular organization.
Risk Factor of not implementing an Information Security System in your Organization
Risk is higher is one organization doesn’t setup an information security system in his or her company. Major risk is of administrative control. If the security is low then one can gain access over whole the system and he or she gets the administrative rights in his hand. If it happens then it can destruct whole organization as well as he can breach the data of company. He or she can take over the control of the whole organization. Administrative controls are generally known as procedural controls. Other major risk of not hiring the information security is reputation. If data breach occurs by the malicious attack from the attacker, it can affect company’s share holders as well as on the financial department. It can also degrade the reputation of the organization.
Information Security Tips for the users or the clients
This was all about the organization’s Security. Talking about the client side security, clients are generally the customers or the ordinary internet users. Here we have mentioned some tips and the tricks which should be given high priority to avoid the breaching.
General Tips / Internet Tips: Gaming and internet devices are connected to internet now. This should be kept in mind of all gamers and developers. So make sure about your private sensitive data like username password, game consoles and other. Everyone must use hardware as well as software technologies to protect USB devices. Keep in mind that free antivirus software doesn’t give full protection so always buy a license version antivirus for online protection. Every parent should keep their eye on their child that what and which kind of activity he or she is doing online. Always be habited to keep a back up of your all important information or the data.
Awareness of Well known Attacks to users (Social Engineering Attacks):
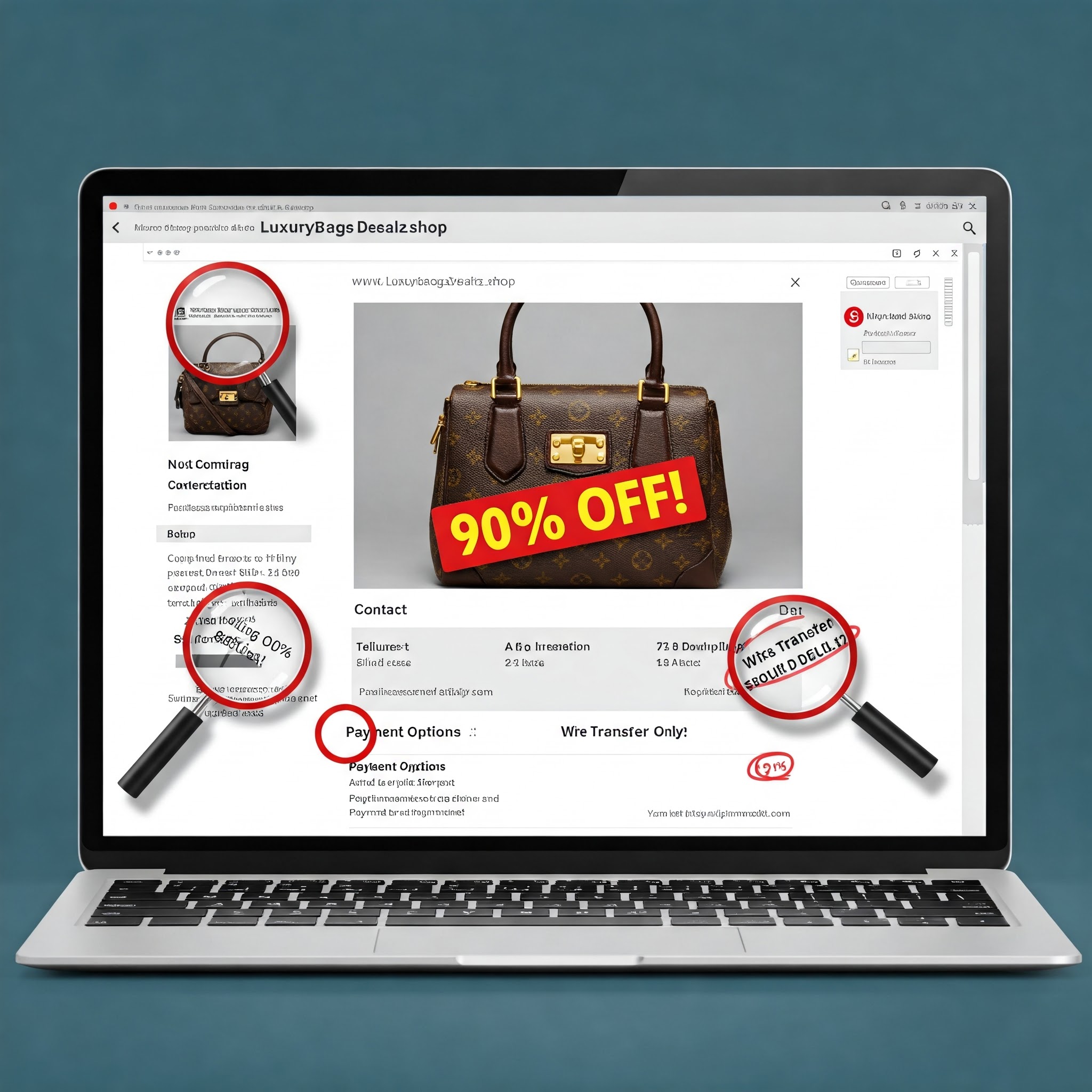
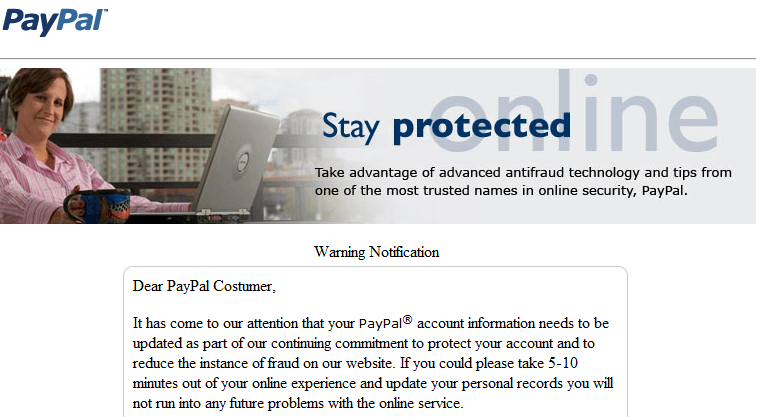
Phishing / Fake Login Page: This is used to attack human’s mind. Generally in this method attacker makes a page exactly as any of the organization. For example Attacker makes a Face book login page exactly as Real face book login page. But its URL will quite different like this nowadays people don’t pay more attention to the URL like faacebook.com or facebo0k.com and they just log in into their account. In this case this phishing or the fake page login helps the attacker to get the email ids and the passwords of the users. One time hard work but after that it gives mass usernames and passwords to the attacker. Fake Programs: In this attack fake programs are generated which can be in a form of executable files. Lay out, the design of the program and the name of the program is created in such a way that it can take a place in human mind. If it is delivered to use it will ask for the one time authentication and it will ask for the ID and password of a particular account. User provides it to the software and he/she things now he/she is able to use the software. But it won’t happen like that. Once Id password are provided to the software it will immediately sent to the attacker or the creator of that fake tool and thus it gets compromised. There are many tools available on the internet like yahoo hacker, Gmail password hacker, and face book hacker. Key loggers: Key loggers are the advance technique used worldwide now days for hacking sensitive information. They are the simple tools which records every keystrokes of the keyboard. One a victim has opened real accounts his/her id password will be recorded. And in the case of the remote key logger, the recorded id password will be sent to particular mail of the attacker.
Mobile Banking and Mobile Security Tips: Mobile banking always uses wireless technology. Organization should implement 2 factors or 2 way authentication system in their organization in which if attacker got passed in attacking the 1st factor, he or she will still need the personal information to gain access over Victim’s whole account. Organization should implement the monitoring system on the high transaction. So any terror attack is going to be happen and if there will be any financial transaction going to be take place, it can be detected.
To put in a nutshell, Information security is an essential part of the organization to protect their organization. Every big or small company should have a network administrator or the security engineer. It also affects on the reputation of the organization.









Be the first to comment