
From 2014 to 2015, tech support scams increased by 200%, according to cybersecurity leader Symantec in their 2016 Internet Security Threat Report.
Throwing around scary cybersecurity terms like “malware,” scammers try to frighten victims on the phone and convince them that their computer and personal information are at risk. Acting like an expert from a trusted organization, the caller then persuades the victim to download an application or visit a site to resolve the issue, actually delivering ransomware to the unaware victim’s computer.
Here’s an example of a tech support scam I recently experienced during the workday (and how I gracefully handled it).
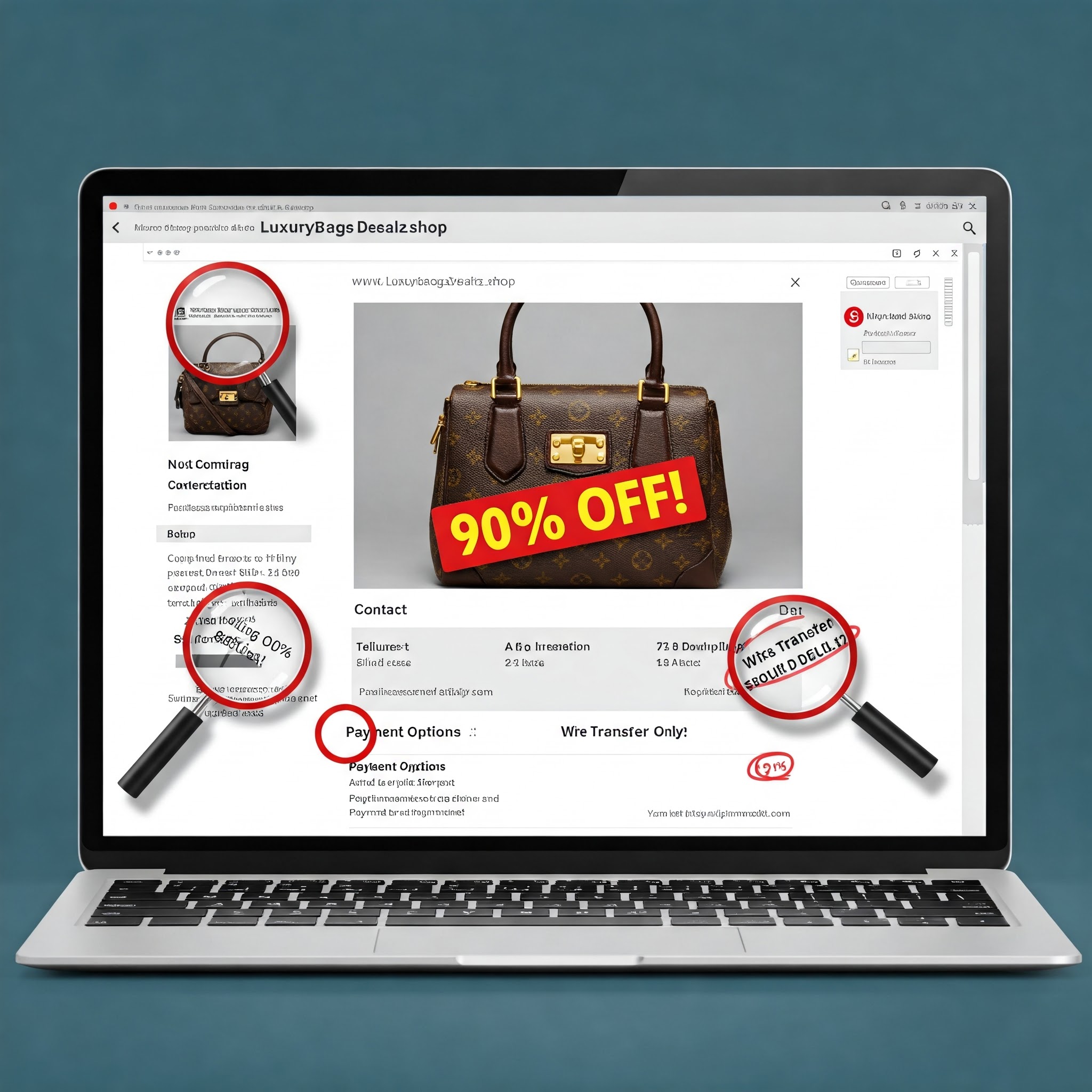
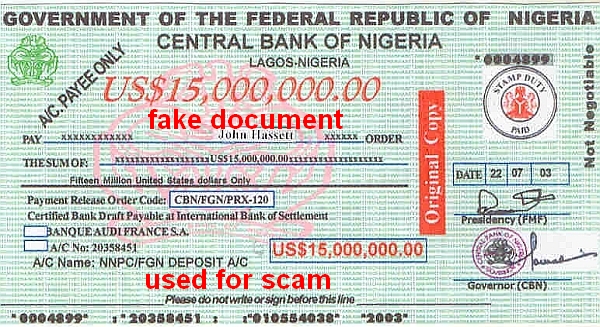
About 10 minutes before our all-hands team call ends, I get a phone call from “private number.” I never know who these callers are. I’m always worried that it is some relative of a Nigerian prince needing to borrow thousands of dollars so I can become really, really wealthy and rent the red Porsche that the car rental company keeps wanting me to drive when I come to the VMware AirWatch office in Atlanta.
The gentlemen on the other end of the phone identifies himself as Smith Hamilton from the Network Security Department. He tells me that there has been a great deal of network traffic attempting to get into my computer. Faraway computers from Georgia, North Carolina and Iowa have been trying to maliciously access the private information on my computer, he says.
I tell him my girlfriend is calling me and ask if I can put him on hold. I walk over to the kitchen and make myself a peanut butter and jelly sandwich (I really need that Nigerian prince’s family member to call me). After cleaning up my mess, I walk back and take Mr. Hamilton off hold. He is patiently waiting. This guy must really want to protect my personal information for me. What a saint.
We start talking, and he asks me to go to “the Google website” and search for a certain online meeting software. I ask him what browser I should be using: Dolphin or Opera? I tell him my wife prefers Opera, and my girlfriend says that Dolphin is the best. He can’t believe I have both a wife and a girlfriend and suggests that I should leave one of them. (I never tell him that they are the same person.) He lectures me about wedding vows and says that I should search my soul and do the right thing. This guy is a saint.
I ask if I can put him on hold because the doorbell rang. I say if I’m not back in five minutes then it means that my girlfriend is at the door and that he probably should hang up because no good things happen when she’s at the door. I review the PowerPoint slides that my colleague sent. After four and a half minutes, I reconnect with Mr. Hamilton.
He stops lecturing me, and guides me through installing the business application I searched for on my “Windows machine.” I read an email from my boss asking me to get back to work. I tell Mr. Hamilton that he can call me back tonight after 10 p.m. when my wife goes to sleep, and we can talk more about his qualms with my personal life.
Handle Tech Support Scams like a Cybersecurity Champ
Now, I’m off to see if I can find an application for him to install on his computer to help make my “Windows machine” faster. I’ll have a clean virtual machine set up and waiting for Mr. Hamilton if he calls me back. I’ll waste his time all night long if I need to, because it keeps him from calling and abusing someone else.
If you find yourself on the phone with a Mr. Hamilton, hang up. You should never accept the help of these “altruistic helpers.” No one is ever going to call you and help you remove malware from your computer. No one is ever going to call you and help you speed up your computer for free.
Microsoft offers some sound advice on avoiding tech support scams here. You can also log a complaint with the Federal Trade Commission (FTC) here.








Be the first to comment