Business Identity Theft: A Growing Threat to Businesses of All Sizes
One of the most serious threats to businesses is business identity theft (BIT), which occurs when criminals steal the identifying information of a business to commit fraud. BIT can have devastating consequences for businesses, including financial losses, damage to their reputation, and even legal liability. In today’s interconnected world, businesses of all sizes are increasingly vulnerable to cybercrime.
What is Business Identity Theft?
Business identity theft is a crime in which criminals use a business’s identifying information, such as its Employer Identification Number (EIN), tax identification number, or business name, to commit fraud. Criminals can use this information to open fraudulent bank accounts, obtain credit cards, apply for loans, or even file fraudulent tax returns.
How Does Business Identity Theft Occur?
There are many ways in which criminals can steal a business’s identity. Some of the most common methods include:
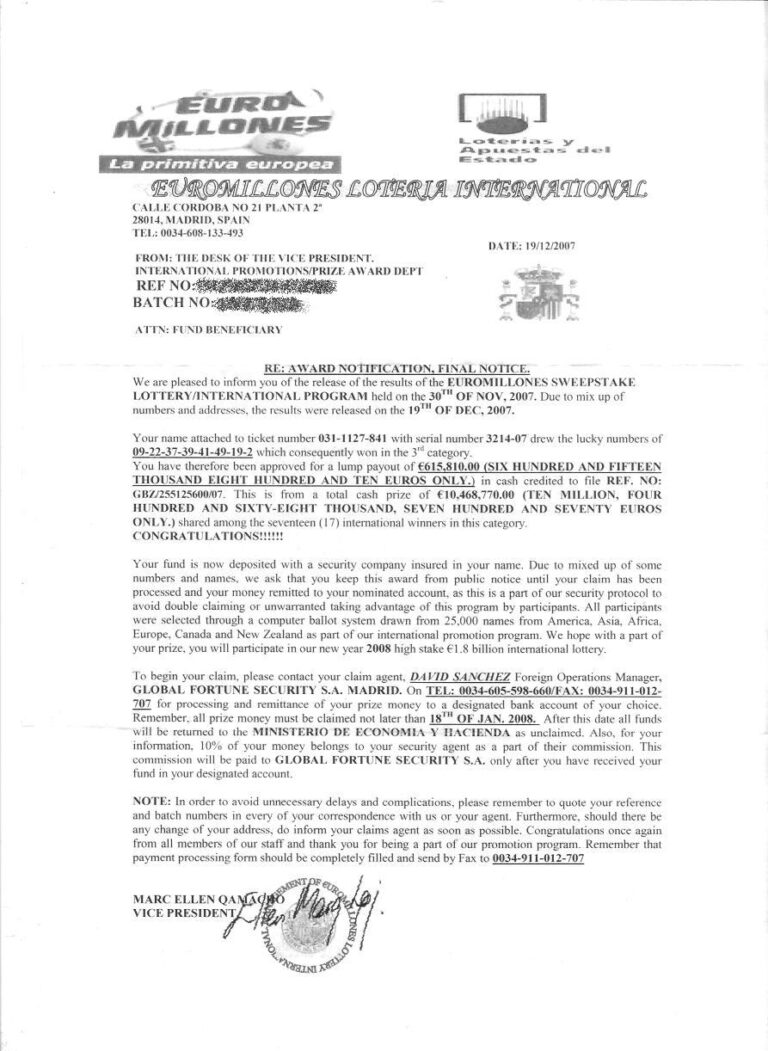
- Phishing scams: Criminals send emails or text messages that appear to be from a legitimate organization, such as a bank or credit card company. These emails or text messages often contain links that, when clicked, take the victim to a fake website that looks like the legitimate organization’s website. Once the victim enters their personal information on the fake website, the criminals can steal it.
- Data breaches: Criminals can hack into a business’s computer system and steal its data, including its identifying information. Data breaches can also occur when employees accidentally expose a business’s data.
- Social engineering: Criminals can trick a business’s employee into revealing their identifying information. This can be done by posing as a customer or vendor, or by using other methods to gain the employee’s trust.
What are the Signs of Business Identity Theft?
Business identity theft (BIT) is a serious crime that can have a devastating impact on businesses of all sizes. Here are some of the key signs that your business may have been a victim of BIT:
Unexpected Changes in Bank Account or Credit Card Statements
- Unexpected charges on your business’s bank account or credit card.
- Payments to companies or individuals you don’t recognize.
- Deductions for services you didn’t request or receive.
Collections Letters for Debts You Don’t Owe
- Collections letters for debts that your business doesn’t owe.
- Threats of legal action or wage garnishment.
- Calls from debt collectors claiming to represent your business.
Fraudulent Tax Returns Filed in Your Business’s Name
- Letters from the IRS informing you that a fraudulent tax return has been filed in your business’s name.
- Audits by the IRS.
- Problems with your business’s tax refund.
Unexplained Changes in Your Business’s Credit Report
- New accounts opened in your business’s name.
- Debts added to your business’s credit report that you don’t recognize.
- Changes to your business’s credit score that you can’t explain.
Employees Reporting Suspicious Activity
- Employees receiving emails or phone calls that appear to be from legitimate businesses, but are actually phishing scams.
- Employees noticing unauthorized access to their business’s computer system.
- Employees discovering that their personal information has been compromised.
Data Breach Notifications
- Receipt of a data breach notification from a third-party vendor that your business does business with.
- Reports of a data breach in the news that may have affected your business.
- Changes to your business’s security measures as a result of a data breach.
What Can Businesses Do to Protect Themselves from Business Identity Theft?
Shielding Your Business from the Ravages of Identity Theft
In today’s digitally driven world, businesses are not immune to the perils of identity theft. Just as individuals can have their personal information compromised, businesses face the same risk, with potentially devastating consequences. Business identity theft occurs when criminals steal sensitive information, such as an Employer Identification Number (EIN), bank account numbers, or customer data, to impersonate a company for fraudulent purposes.
The repercussions of business identity theft can be severe, ranging from financial losses and reputational damage to legal ramifications and even business failure. Therefore, it is imperative for businesses to take proactive measures to safeguard their identity and protect themselves from this growing threat.
Establishing a Robust Defense: Essential Steps to Protect Your Business
- Employ Strong Passwords and Multi-Factor Authentication: Enforce strong password policies, mandating complex passwords and regular password changes. Implement multi-factor authentication (MFA) for all accounts, adding an extra layer of security beyond just passwords.
- Safeguard Sensitive Data: Securely store and manage sensitive data, including customer information, financial records, and employee data. Use encryption, access controls, and data loss prevention (DLP) tools to protect sensitive files both at rest and in transit.
- Educate Employees: Train employees to recognize and avoid phishing scams and social engineering attacks. Emphasize the importance of password security and data protection. Conduct regular cybersecurity awareness training sessions to keep employees updated on the latest threats.
- Implement Secure Email Practices: Use secure email encryption protocols like TLS/SSL to protect sensitive communications. Educate employees on identifying email phishing attempts and reporting suspicious emails promptly.
- Monitor Accounts and Transactions Regularly: Establish regular monitoring of bank accounts, credit card statements, and customer transactions to detect any unauthorized activity or fraudulent charges. Promptly report any suspicious activity to the relevant authorities.
- Secure Physical Documents: Securely store and dispose of physical documents containing sensitive information. Use shredding machines to destroy confidential documents when no longer needed.
- Stay Vigilant and Update Security Measures: Stay informed about the latest cybersecurity threats and vulnerabilities. Regularly update security software, operating systems, and applications to address newly discovered threats.
- Establish a Comprehensive Incident Response Plan: Develop a comprehensive incident response plan to effectively manage and mitigate the impact of a potential identity theft breach. This plan should include clear communication protocols, data recovery procedures, and notification processes.
- Consider Cyber Insurance: Evaluate the viability of cyber insurance to protect your business from potential financial losses arising from identity theft or data breaches.
- Seek Expert Guidance: Consult with cybersecurity experts to conduct regular risk assessments, identify potential vulnerabilities, and implement appropriate security measures tailored to your business’s specific needs.
Business identity theft, also known as corporate or commercial identity theft, is a type of fraud that involves a criminal stealing a company’s identifying information and using it to conduct fraudulent activities. This can include opening new accounts in the company’s name, making unauthorized purchases, and even taking out loans.
Key Characteristics of Business Identity Theft:
Business identity theft (BIT) has become a growing threat to businesses of all sizes, as criminals seek to exploit their valuable identifying information for financial gain and other malicious purposes. Understanding the key characteristics of BIT is crucial for businesses to effectively identify, prevent, and mitigate its impact.
1. Prevalence across Business Sizes
BIT does not discriminate against business size; it can affect small startups, established enterprises, and even large multinational corporations. The prevalence of BIT stems from the fact that businesses of all sizes hold essential information that criminals desire. Whether it’s financial records, employee data, or business creditworthiness, criminals can exploit this information to their advantage.
2. Severe Financial Consequences
BIT can inflict significant financial damage on businesses. Criminals may open fraudulent accounts, obtain credit cards, or apply for loans in the business’s name, leaving the company liable for debts it never incurred. These actions can drain the company’s resources, disrupt operations, and potentially lead to bankruptcy.
3. Reputational Damage and Loss of Customer Trust
The negative impact of BIT extends beyond financial losses. Once a business becomes a victim of BIT, its reputation can suffer irreparable damage. Customers may become wary of dealing with the company, fearing that their personal information is at risk, leading to a decline in business and lost revenue.
4. Potential Legal Liability Issues
Businesses that fall prey to BIT may face legal consequences stemming from the fraudulent activities committed in their name. If criminals use the company’s information to file fraudulent tax returns, open delinquent accounts, or engage in other illegal activities, the business could be held liable for the consequences.
5. Diverse Methods Employed by Criminals
Criminals employ a variety of sophisticated techniques to steal business identities and execute their fraudulent schemes. These methods include:
- Phishing Attacks: Phishing emails or text messages disguised as legitimate communications from banks, credit card companies, or other businesses entice users to click on malicious links or provide sensitive information.
- Data Breaches: Hackers infiltrate business computer systems or gain access to physical records to steal sensitive data, including business names, EINs, tax IDs, and financial statements.
- Social Engineering: Criminals manipulate or deceive employees into revealing confidential information through impersonation, deceptive requests, or creating a sense of urgency.
6. Proactive Measures for Prevention:
Businesses can significantly reduce their vulnerability to BIT by implementing preventive strategies:
- Employee Training: Educate employees about BIT, phishing scams, and social engineering tactics to enhance their vigilance and ability to identify suspicious activities.
- Strong Password Policies: Enforce strong password requirements for all business accounts and require regular password changes to minimize the risk of unauthorized access.
- Data Security Measures: Install robust firewalls, anti-virus software, and data encryption protocols to protect business systems and sensitive information from cyber threats.
- Regular Credit Monitoring: Regularly monitor business credit reports to detect any unauthorized activity or fraudulent accounts opened in the company’s name.
- Data Breach Response Plan: Develop a comprehensive data breach response plan to address any security breaches effectively, including notifying affected parties, conducting investigations, and implementing corrective measures.
By understanding the key characteristics of BIT and implementing proactive measures, businesses can significantly reduce their exposure to this insidious threat and protect their valuable assets, financial health, and reputation.
Impact of Business Identity Theft:
Business identity theft (BIT) is a serious crime that can have a devastating impact on businesses of all sizes. Here are some of the key impacts of BIT:
Financial Losses:
BIT can cause significant financial losses for businesses. Criminals can use stolen business information to open fraudulent bank accounts, obtain credit cards, apply for loans, and even file fraudulent tax returns in the business’s name. These activities can lead to significant debt for the business, which can damage its credit rating and make it difficult to obtain financing in the future.
Reputational Damage:
BIT can also damage the reputation of a business. If customers learn that a business has been the victim of identity theft, they may be hesitant to do business with the company. This can lead to a loss of customers, revenue, and market share.
Legal Liability:
In some cases, businesses that are victims of BIT may be held liable for the fraudulent activities committed in their name. This can include paying for debts that the business did not incur, defending itself against lawsuits, and even facing criminal charges.
Operational Disruption:
BIT can also disrupt a business’s operations. For example, if a business’s bank accounts are frozen or its credit is damaged, it may be unable to pay its bills or make payroll. This can lead to employee layoffs, business closures, and even bankruptcy.
Increased Insurance Costs:
Businesses that have been victims of BIT may also face increased insurance costs. This is because insurance companies are more likely to view these businesses as higher risks.
Lost Productivity:
Employees may also experience lost productivity if they are concerned about the possibility of BIT. This is because they may be distracted from their work and worried about their personal information being stolen.
Damage to Employee Morale:
BIT can also damage employee morale. If employees believe that their company is not taking their concerns about security seriously, they may lose faith in the company and be more likely to quit.
Impact on Brand Image:
A business’s brand image can be severely damaged if it is the victim of BIT. This is because the public may perceive the business as being incompetent or untrustworthy.
Increased Regulatory Oversight:
In response to the increasing prevalence of BIT, governments around the world are imposing new regulations on businesses. This can increase the cost of doing business and make it more difficult for businesses to comply with regulations.
In addition to these direct impacts, BIT can also have a number of indirect impacts on businesses. For example, BIT can make it difficult for businesses to recruit and retain employees, and it can make it more difficult for businesses to access credit or other financing.
Prevention Strategies for Businesses:
- Strong Passwords and Multi-Factor Authentication (MFA): Enforce complex password policies and implement MFA for all accounts to add an extra layer of security beyond passwords.
- Data Security Measures: Securely store and manage sensitive data using encryption, access controls, and data loss prevention (DLP) tools to protect both stored and transmitted data.
- Employee Education: Train employees to recognize and avoid phishing scams, social engineering attacks, and other common tactics used to steal sensitive information.
- Secure Email Practices: Employ secure email encryption protocols and educate employees on identifying and reporting suspicious emails.
- Regular Account Monitoring: Regularly monitor bank accounts, credit card statements, and customer transactions to detect any unauthorized activity or fraudulent charges promptly.
- Secure Physical Documents: Securely store and dispose of physical documents containing sensitive information using shredding machines when no longer needed.
- Cybersecurity Updates: Stay informed about the latest cybersecurity threats and vulnerabilities. Regularly update security software, operating systems, and applications to address newly discovered threats.
- Incident Response Plan: Develop a comprehensive incident response plan to effectively manage and mitigate the impact of a potential identity theft breach.
- Cyber Insurance Evaluation: Consider cyber insurance to protect your business from potential financial losses arising from identity theft or data breaches.
- Expert Guidance: Consult with cybersecurity experts to conduct regular risk assessments, identify potential vulnerabilities, and implement appropriate security measures tailored to your business’s specific needs.
Draft Bvolume_up
Business identity theft, also known as corporate or commercial identity theft, occurs when criminals impersonate a company to illegally transact business, obtain credit, or acquire loans in the business’s name. This malicious act is often perpetrated to gain financial benefits at the expense of the victim business.
Common Methods of Business Identity Theft
Criminals employ various methods to steal a business’ identity:
- Phishing Attacks: Phishing emails and websites mimic legitimate business communication to trick individuals into revealing sensitive information, such as company login credentials or financial data.
- Social Engineering: Social engineering techniques exploit human vulnerabilities to gain access to confidential information or manipulate individuals into making unauthorized actions.
- Data Breaches: Data breaches, often stemming from security vulnerabilities or human error, expose sensitive business data to unauthorized access.
- Misrepresenting Identity: Criminals may pose as legitimate business representatives to establish new accounts, obtain loans, or negotiate contracts.
Detrimental Consequences of Business Identity Theft
The impact of business identity theft extends beyond financial losses:
- Financial Damage: Businesses may face steep debt burdens, legal fees, and reputational damage due to fraudulent activity.
- Legal Ramifications: Businesses may be held liable for fraudulent actions committed in their name, leading to legal disputes and penalties.
- Reputational Damage: The unauthorized use of a business’ identity can tarnish its reputation, erode customer trust, and hinder future business opportunities.
Protective Measures to Shield Businesses from Identity Theft
Prevention is crucial to safeguard businesses from identity theft:
- Strong Security Practices: Employ strong passwords, multi-factor authentication (MFA), and data encryption to protect sensitive information.
- Regular Data Audits: Conduct regular audits of business data to identify and address potential vulnerabilities.
- Employee Education: Train employees on recognizing phishing scams, social engineering tactics, and data protection protocols.
- Secure Document Storage: Securely store and dispose of physical documents containing sensitive information.
- Vendor Due Diligence: Thoroughly vet and monitor third-party vendors to minimize data exposure risks.
- Cyber Insurance: Consider cyber insurance to mitigate financial losses and legal expenses arising from identity theft incidents.
- Risk Assessments: Regularly conduct risk assessments to identify and prioritize cybersecurity threats.
- Incident Response Plan: Develop a comprehensive incident response plan to effectively address and recover from identity theft breaches.
- External Consultation: Seek guidance from cybersecurity experts to tailor security measures to specific business needs.
By implementing these preventive measures, businesses can significantly reduce their vulnerability to business identity theft and protect their valuable assets.
What to Do If You Think Your Business Has Been a Victim of Identity Theft
If you think your business has been a victim of identity theft, it is important to act quickly. Here are the steps you should take:
1. Document the theft: Keep a detailed record of everything you know about the theft, including the date it occurred, the type of information that was stolen, and any other relevant details. This documentation will be helpful in your investigation and recovery efforts.
- Keep track of receipts, invoices, and other records related to the theft.
- Take screenshots of any suspicious emails or websites you received.
- Keep a record of any calls you made to banks, credit card companies, or other businesses.
2. Contact your bank and credit card companies: Immediately notify your bank and credit card companies about the theft. They can help you put a fraud alert on your accounts and cancel any unauthorized charges.
- Contact each of your banks and credit card companies to report the theft.
- Provide them with the information you documented in step 1.
- Ask them to cancel any unauthorized charges and place a fraud alert on your accounts.
3. File a police report: Filing a police report is important for documenting the theft and potentially recovering your losses. You may also need a police report to file a claim with your insurance company.
- Contact your local police department and file a report.
- Bring documentation of the theft with you, such as receipts, invoices, and screenshots.
4. Place a fraud alert on your credit report: A fraud alert will notify creditors to take extra precautions when approving new accounts in your name. You can place a fraud alert online, by phone, or by mail.
- Visit the website of one of the three major credit bureaus: Equifax, Experian, or TransUnion.
- Complete the fraud alert request form.
- Provide them with the information you documented in step 1.
5. Contact the Federal Trade Commission (FTC): The FTC is a government agency that can help you recover from identity theft. They can provide you with resources and support, and they can help you file a complaint against the identity thief.
- Visit the FTC website: https://www.identitytheft.gov/
- File a complaint online.
- Provide them with the information you documented in step 1.
6. Take steps to protect your business: Once you have taken these steps, you can start to take steps to protect your business from future identity theft. This includes educating your employees about identity theft, implementing stronger security measures, and monitoring your credit reports regularly.
Here are some additional resources that can help you:
- The Identity Theft Resource Center: https://www.identitytheft.gov/
- The National Association of Consumer Credit Management (NACCM): https://notavictim.org/
- The Social Security Administration: https://www.ssa.gov/
Remember, identity theft is a serious crime, but it is also a preventable one. By taking steps to protect your business, you can help to minimize your risk of becoming a victim.
Resources for Businesses
Here are some of the key resources available to help businesses protect themselves from business identity theft (BIT):
Government Agencies
- Federal Trade Commission (FTC): The FTC is a leading resource for businesses seeking information and guidance on preventing and responding to BIT. Their website provides a wealth of resources, including tips for protecting business information, sample policies, and steps to take in the event of a data breach. https://consumer.ftc.gov/features/identity-theft
- Small Business Administration (SBA): The SBA offers a variety of resources to help businesses of all sizes improve their cybersecurity and protect themselves from cyber threats, including BIT. Their website provides toolkits, guides, and webinars on topics like password management, data security, and phishing scams. https://www.sba.gov/funding-programs/loans/covid-19-relief-options/reporting-identity-theft
Industry Organizations
- National Cybersecurity Alliance (NCSA): The NCSA is a non-profit organization that provides cybersecurity awareness and education programs to businesses and individuals. Their website offers resources on BIT prevention, including training modules, checklists, and case studies. https://staysafeonline.org/
- Business Alliance to Safeguard Electronic Commerce (BASCE): BASCE is a trade association that promotes cybersecurity and privacy in the business community. Their website provides resources on BIT prevention, including a data breach simulator, best practices guidelines, and compliance checklists. https://…
- Association of Corporate Counsel (ACC): The ACC is a professional organization for corporate lawyers. Their website provides resources on BIT prevention, including legal updates, compliance tools, and case studies. https://www.acc.com/
Security Software and Services
- Verizon Business: Verizon offers a comprehensive suite of cybersecurity solutions for businesses of all sizes, including anti-virus software, data loss prevention, and incident response services. https://www.verizon.com/business/my-business/
- Cisco: Cisco offers a wide range of security products and services for businesses, including firewalls, intrusion detection systems, and virtual private networks (VPNs). https://www.cisco.com/c/en/us/solutions/small-business.html
- Palo Alto Networks: Palo Alto Networks specializes in network security solutions, including firewalls, intrusion prevention systems, and cloud security services. https://www.paloaltonetworks.com/
In addition to these resources, businesses can also consider implementing the following best practices to protect themselves from BIT:
- Educate employees about BIT risks and how to identify phishing scams and other suspicious activity.
- Implement strong password policies and require regular password changes.
- Use strong encryption to protect sensitive data.
- Scan your systems regularly for malware and other security threats.
- Monitor your credit reports for any unauthorized activity.
- Have a plan in place to respond to a data breach.
By taking these steps, businesses can significantly reduce their risk of becoming victims of BIT and protect their valuable information.